Want a heads up when a new story drops? Subscribe here.
AI is one of the best tools in any marketer’s hands right now. At Socialfix, we use it every single day. We use it to research audiences, to draft outreach, to identify podcast opportunities for clients, to process data that would have taken a team of analysts a week to work through. We are genuine believers. The efficiency is real, the creative range is wide open, and the agencies that build smart AI workflows into their operations are already pulling ahead of the competition.
But here is what too few people want to say out loud: the same technology making your marketing team faster and sharper is making criminals smarter, more patient, and far harder to dismiss at first glance. AI does not have a conscience. It does not care whether it is booking your client a legitimate podcast appearance or running a con designed to drain a small business owner’s bank account and hijack their social media presence before they realize what happened.
This past week, one of those cons landed in our client’s inbox. She is a fitness, nutrition, and wellness expert with around 35,000 engaged Instagram followers and a track record of real media appearances. The invitation looked credible. The email thread was patient and well-constructed. And if she had not had an experienced PR team behind her, it would have cost her approximately $2,500 and possibly her Facebook page.
Here is exactly what happened, how we caught it, and what every entrepreneur building a brand in 2026 needs to know before they end up in the same crosshairs.
Table of Contents
How Bad Is the AI Threat Right Now? The Numbers Make the Case
Before getting into the specifics of this case, you need to understand the environment we are all operating in. This is not a niche problem for celebrities or Fortune 500 security teams. It is a mass-market, automated, industrialized fraud operation running at a scale that was impossible just two years ago.
According to Vectra AI’s 2026 analysis, AI-powered scams surged 1,210% in 2025, while traditional fraud grew at 195%. Those are not comparable rates. That is a fundamentally different category of threat. The same report projects AI-driven fraud losses reaching $40 billion by 2027, and the World Economic Forum’s Global Cybersecurity Outlook 2026 found that 73% of organizations were directly affected by cyber-enabled fraud in 2025. The barriers to entry have collapsed entirely. Group-IB’s documented research shows that a sophisticated, personalized, multi-touch scam operation now costs an attacker roughly $30 to $200 per month in dark web AI subscriptions. Anyone with an internet connection and a small budget can now run the kind of targeted social engineering campaign that once required serious criminal infrastructure.
The specific capability that makes email-based scams so dangerous today is what security researchers call LLM-powered phishing. Large language models generate hyper-personalized outreach that references specific details about the target, mirrors professional communication styles, and unfolds across multiple exchanges in a way that reads entirely human. These are not the poorly spelled Nigerian prince emails from fifteen years ago. They are well-researched, patient, multi-step operations that build genuine trust before they move in for the ask.
Voice is its own story. McAfee’s research established that three seconds of audio is enough to create a voice clone with 85% accuracy. Fortune reported in late 2025 that voice cloning has crossed what researchers call the indistinguishable threshold, meaning average listeners can no longer reliably tell the difference between a cloned voice and a real one. When a scammer moves the conversation from email to a Zoom call staffed by an AI voice bot, that is not an escalation of clumsiness. That is the closing move of a well-designed operation.
What Actually Happened: A Real Attack, Documented

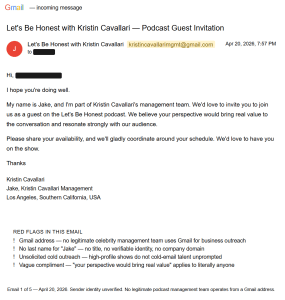
Our client received an email on April 20th from an address presented as the management team behind a major lifestyle and wellness podcast hosted by a well-known public figure. That public figure is real, her podcast is real, and she is completely innocent here. Her name and show are being used without her knowledge or consent, a pattern that has been documented across multiple celebrity podcasts and public figures in this exact scam format. The email was signed by someone named “Jake,” presenting as a talent coordinator who wanted to invite our client on as a guest.
Read that first email cold and your initial reaction, especially as someone actively building a brand, is probably excitement. The tone is professional. The language is measured and appropriate. The compliment is targeted enough to feel considered rather than generic. What the AI had done before sending that email was research our client: her niche, her background, her positioning, the kind of invitation she would take seriously. The outreach was built around that profile before a single word was written.
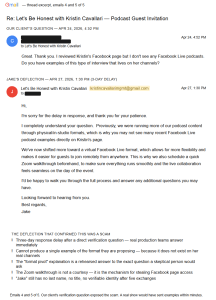
Over the following days, the scam ran across five email exchanges. When our client asked whether the appearance would be virtual or in-person, “Jake” came back with a full production window: 10 episodes planned between May 11th and May 30th, sessions running 45 minutes to an hour, an open invitation to choose dates that worked for her schedule, and a warm note about keeping the conversation authentic and unscripted. It reads like a real show’s standard guest brief. The scheduling specificity, the casual reassurance about no formal scripts, the collaborative tone, all of it reflects how legitimate podcast coordination actually sounds. The AI had clearly been trained on the real thing.
When our client confirmed availability from May 26th to 30th, the response the next morning confirmed those dates and revealed the format: a virtual Facebook Live event. She would go live from her own Facebook page while the host broadcast from theirs. Before the live session, there would be a Zoom walkthrough to make sure everything ran smoothly. That is the mechanism. That is where the scam lives.
Our client did exactly the right thing. She asked for examples of this format on the real host’s public channels, noting she had reviewed the actual Facebook page and found no evidence of Facebook Live podcasts. Jake’s reply came two days later with a prepared explanation: the show had recently shifted toward virtual Facebook Live from its previous in-studio format, which is why recent examples were difficult to find online. The response was polished and ready. It was designed to answer precisely the question a skeptical person would ask. The conversation never reached a Zoom call because we had already confirmed this was a scam.
The Signals That Gave It Away
None of what we caught required special technology or a cybersecurity background. It required industry knowledge, pattern recognition, and the discipline to be skeptical of flattering news.
The first signal was the nature of the opportunity itself. Anyone who works in podcast PR understands how hard legitimate top-tier placements are to earn. You pitch, you follow up, you build relationships over months, you wait. A high-profile lifestyle show does not cold-email a fitness coach on a Sunday evening because they stumbled across her Instagram. That is not how this works. High-profile podcast invitations happen because of a recent newsworthy event, a warm introduction through a shared network, or a long-standing relationship with someone connected to the show. An unsolicited cold inbound from a major show is rare enough that your first response should be verification, not excitement.
The Gmail address is not a yellow flag. It is a disqualifying one. Any real production company or management team operating at the level of a nationally recognized podcast runs outreach from a branded domain. Full stop. A Gmail address from a supposed national podcast management company is the tell. Setting up a domain email takes twenty minutes and costs approximately twelve dollars a year. The fact that they did not do it tells you they are running a high-volume operation across hundreds of targets where catching a few sharp-eyed people costs them nothing.
The Facebook Live format is where the operational lie becomes visible. We know the actual podcast. It is professionally produced, recorded in-studio, distributed across major platforms. It does not run as a Facebook Live event. When you have completed enough real podcast placements to know what a show’s production model actually looks like, a convenient format shift that requires your client to go live from her own Facebook page is not a credible explanation. It is the payload. The Facebook Live structure means the scam operation leaves no trace on their end: no camera, no verifiable identity, no permanent record, and access to your social media infrastructure if you follow the instructions during the “tech setup.”
“Jake” does not exist in any verifiable form. No last name, no LinkedIn profile, no provable presence anywhere online. Real talent coordinators are findable. Real management teams have websites, domain emails, and staff who appear in professional search results. The absence of a verifiable human behind the outreach is not a gap in their communications process. It is an operational requirement for running this at scale.
What Was Waiting on That Zoom Call
Our client never got on the call. But we know exactly what was waiting there because multiple entrepreneurs and content creators who did fall for similar operations have documented their experiences in detail.
Writer and photographer Dina Litovsky published a first-person account of nearly being caught in an identical process: a polished invitation, a Facebook Live format, a Zoom tech check, a voice on the other end with no camera turned on. During that call, the AI voice bot walked her through her Facebook Business Suite settings, directing her to add an email address under the guise of enabling Facebook Live. The actual goal was access to her page’s administrator settings. The moment you follow those instructions, you have handed a stranger control of your business’s social presence.
A Better Business Bureau investigation documented the same playbook in more clinical terms: during the Zoom tech check, targets are directed to download software, enter codes, or navigate to pages designed to capture credentials. Once the attackers have access, they change passwords and lock the legitimate owner out. From that point, the compromised account serves as a platform for fraudulent advertisements, scam content pushed to an established and trusting audience, or direct financial extraction from followers who recognize the brand.
The voice bot operates without a camera because it does not need one. Its job is to be warm, informed, and convincing for twenty to thirty minutes. It knows details about the target because the AI scraped that information before the first outreach email was written. The flattery in the initial email is not accidental. It is engineered based on a profile assembled from public sources before any human interaction began.
The version of this scam that targeted our client appears to run a slightly different closing move from the credential-theft model. Based on documented cases from others who went through the full process, the Zoom call ends with an opportunity that transforms into a payment request: a chance to appear on the actual podcast, which carries a production fee of approximately $2,500. You pay. They disappear. There was never going to be an episode.
Why Your Profile Makes You a Target
This is not random targeting. The people running these operations are not guessing. They are identifying a specific profile, and if you are building a public brand right now, there is a real chance you fit it.
Entrepreneurs and personal brand builders attract this kind of attack for several reasons that compound each other. You are findable. Your name, niche, business model, social following, and media history are all public and scrapeable in minutes. You are motivated. You are actively trying to grow your platform and your business, which means you are primed to act on a credible opportunity quickly. You have something worth taking. A Facebook page with 35,000 followers built over years is a valuable asset to someone who wants to run scam advertisements to an established, trusting audience. And you are usually operating without institutional backup: no legal team reviewing inbound communications, no IT security watching for phishing patterns, no PR team with years of industry experience to tell you this is not how real shows operate.
The targeting precision comes from how much data these operations can pull and process. Social media profiles, podcast databases, media mention trackers, business directories, all of it is accessible through automated scraping. The AI does not just find your email address. It identifies your expertise areas, past appearances, audience size, and any recent press coverage that makes you feel like someone a major show would pursue. Then it constructs an invitation calibrated to what you would most want to receive. A fitness coach gets an invitation from a major wellness show. A business strategist gets invited onto a high-net-worth investor podcast. The hook is always built around the target.
How to Protect Yourself: What Actually Works
None of this requires special software or a security background. It requires the same critical thinking you would apply to any significant business decision.
Check the domain, not just the name. The moment you receive any inbound podcast invitation, look at the actual sending address, not the display name. A real organization sends from its own domain. A Gmail address from a supposed national production company is a scam. This single check, applied consistently, stops the majority of these operations before they get any further.
Research the format against the show’s real track record. Before responding to anything, look at the show’s actual channels. What does their production history look like? Do they run Facebook Lives? Is there any record of the format they are proposing? When someone tells you a major in-studio production has shifted to Facebook Live and cannot produce a single example, that is not a communication gap. It is a fabricated explanation.
Find the human being in the chain and confirm they exist. Search the coordinator’s name. Find their LinkedIn. Look for a company website with verifiable staff. Real people who work for real production companies are findable. If your search returns nothing and the only proof of identity is an email from a Gmail account, there is nobody there.
Know what legitimate inbound actually looks like. Real podcast invitations from established shows come with verifiable show information, a host you can find on Listennotes or Spotify, a production email from a matching domain, and a specific reason they found you: a mutual connection, a recent piece of content, a press mention. The absence of that specificity is itself a signal worth taking seriously.
Apply the too-good-to-be-true standard without apology. A high-profile show reaching out cold on a Sunday evening, offering a guaranteed slot with flexible scheduling and no competitive process, is not how the media world operates. Legitimate opportunities have friction. They require pitching and patience. When that friction disappears completely, the opportunity deserves your skepticism before it gets your calendar.
Frequently Asked Questions
How do I know if a podcast invitation is legitimate?
Start with the email domain. A legitimate podcast production team sends from a branded domain, not Gmail. From there, research the show independently on Spotify, Apple Podcasts, or Listennotes. Confirm that the production format they are proposing matches their actual content history. Search the coordinator by name and verify they have a professional presence you can confirm. Legitimate invitations include specifics about why they found you and what they want to discuss. Generic flattery with no specifics is a clear warning sign.
What is the scam actually trying to get from me?
There are two primary models. The first is credential theft: during a Zoom tech check, the attackers guide you through your Facebook Business Suite settings until you unknowingly grant them administrator access to your page. They lock you out and use your audience to distribute scam content or run fraudulent ads. The second is a pay-to-play scheme: after a convincing multi-email warm-up, you are told that appearing on the actual show requires a production fee, typically around $2,000 to $2,500. Once payment is made, the operation disappears entirely. Both models depend on the same multi-step trust-building sequence.
Why does AI make these scams so much harder to detect than before?
Traditional phishing was detectable by its clumsiness: bad grammar, generic language, obvious pressure. AI-generated outreach has none of those tells. Large language models produce grammatically clean, contextually appropriate, tone-matched communication that reads like it came from a real professional. AI voice bots can conduct full Zoom conversations with no camera, maintaining a warm and informed persona for as long as the call requires. AI-powered data scraping means the outreach is personalized to your specific background and content history before the first email is sent. The result is a scam that passes every surface check most people would run.
Are the celebrities named in these scams involved in any way?
No. The public figures whose names appear in these operations are victims of identity theft, the same as the people being targeted. Their names are chosen because they carry credibility: a real show with a real following that the target can look up and recognize. The actual public figures typically have no knowledge that their brand is being used this way until victims report it. If you encounter this, reporting it to the real show’s verified social accounts helps them alert their actual audience.
What do I do if I think I already fell for one of these scams?
If you shared your screen during a Zoom call or followed instructions to add anyone to your Facebook page administrator settings, act immediately. Change your Facebook password and review your page’s People settings to remove any unauthorized users. Check connected apps in your account security settings and revoke anything unrecognized. If you made a payment, contact your bank or payment processor to initiate a dispute as quickly as possible. File a report with the FTC at reportfraud.ftc.gov. Speed is the only thing that improves your options at that point.
How is this different from a legitimate pay-to-play podcast arrangement?
Legitimate sponsored content or pay-to-play podcast relationships are transparent from the start. A real arrangement is disclosed clearly, comes from a verified organization with a verifiable paper trail, and does not follow a warm-up sequence designed to build emotional investment before the fee appears. When a “free guest appearance” turns into a payment request after multiple trust-building exchanges, treat it as a scam regardless of how credible the earlier emails felt.
What Socialfix Does That Actually Protects Clients
We have been doing PR and podcast guest placement long enough to know exactly how real outreach works, which means we know immediately when something is off. The tell is almost never one single thing. It is a pattern. A Gmail address here, a format that does not match the show’s track record there, a coordinator with no verifiable identity, a scheduling offer that is a little too accommodating. Any one of those in isolation has an innocent explanation. All of them together form a picture that an experienced team reads in minutes.
What happened with our client this week was a reminder that these operations are getting sharper. The email thread we reviewed was genuinely well-constructed. The pacing was patient. The responses to skeptical questions were prepared and plausible. If our client had been managing her own podcast outreach without us behind her, she had a real chance of reaching a Zoom call before the alarm bells got loud enough to act on. The AI voice bot waiting on the other end of that call is specifically designed to handle remaining doubt: warm, informed, and convincing until the moment it walks you through your Facebook settings.
Our job is to stay ahead of this. We track real shows, real production formats, and real coordinators. We know what a legitimate media relationship looks like because we are building them every day. That institutional knowledge caught this scam, not any special technology. The same expertise that makes us effective at earning genuine media placements makes us effective at recognizing the counterfeit versions the moment they appear.
If you are an entrepreneur, an influencer, or a business owner building a personal brand, you need someone in your corner who knows the difference. Not to block every opportunity. Real ones exist and they are worth pursuing. But to make sure the opportunities you pursue are real before you hand over your time, your trust, or your access credentials.
To learn more about how Socialfix approaches PR strategy and media placement for growing brands, explore our PR and influencer marketing capabilities. If you are ready to build a podcast guest strategy that puts you in front of real audiences through real relationships, connect with our team. We know the difference between the real thing and the counterfeit version, and we catch it every time.
References
Litovsky, Dina. “Beware of This Sneaky Podcast Invitation Scam.” Substack, September 24, 2024. https://dinalitovsky.substack.com/p/beware-of-this-sneaky-podcast-invitation
Kantrowitz, Alex. “Beware of the Fake Podcast Invite Scam.” CMSWire, February 18, 2026. https://www.cmswire.com/digital-experience/beware-of-the-fake-podcast-invite-scam/
Bitdefender Hot for Security. “You’re Invited to a Scam: How Fake Podcast Invites Target Content Creators and Small Business Owners.” Bitdefender, August 7, 2025. https://www.bitdefender.com/en-us/blog/hotforsecurity/fake-podcast-invites-target-content-creators-and-small-business-owners
Vectra AI. “AI Scams in 2026: How They Work and How to Detect Them.” Vectra AI, March 23, 2026. https://www.vectra.ai/topics/ai-scams
ScamWatchHQ. “AI-Powered Scams Are Scaling Faster Than Regulation: What to Watch in 2026.” ScamWatchHQ, February 20, 2026. https://scamwatchhq.com/ai-powered-scams-are-scaling-faster-than-regulation-what-to-watch-in-2026/
Podcast Guests. “Watch Out for Podcast Scams: What to Know and How to Stay Safe.” PodcastGuests.com, July 3, 2025. https://podcastguests.com/watch-out-for-podcast-scams-what-to-know-and-how-to-stay-safe/
Findlay, Carly. “I Was Targeted by Scammers Via Podcast Guest Invitations.” CarlyfFindlay.com.au, February 3, 2024. https://carlyfindlay.com.au/2024/02/03/i-almost-got-scammed-via-podcast-guest-invitations/